
In an era where digital threats lurk behind every corner of the internet, the importance of network firewall security cannot be overstated. Firewalls are like digital knights guarding the castle of your enterprise, fending off malicious invaders who seek unauthorized access. Partnering with dedicated IT support services, they form a robust protective shield for your business’s valuable data. In this blog, we delve into the world of firewalls, why they are crucial for businesses, and what makes the best network firewall.
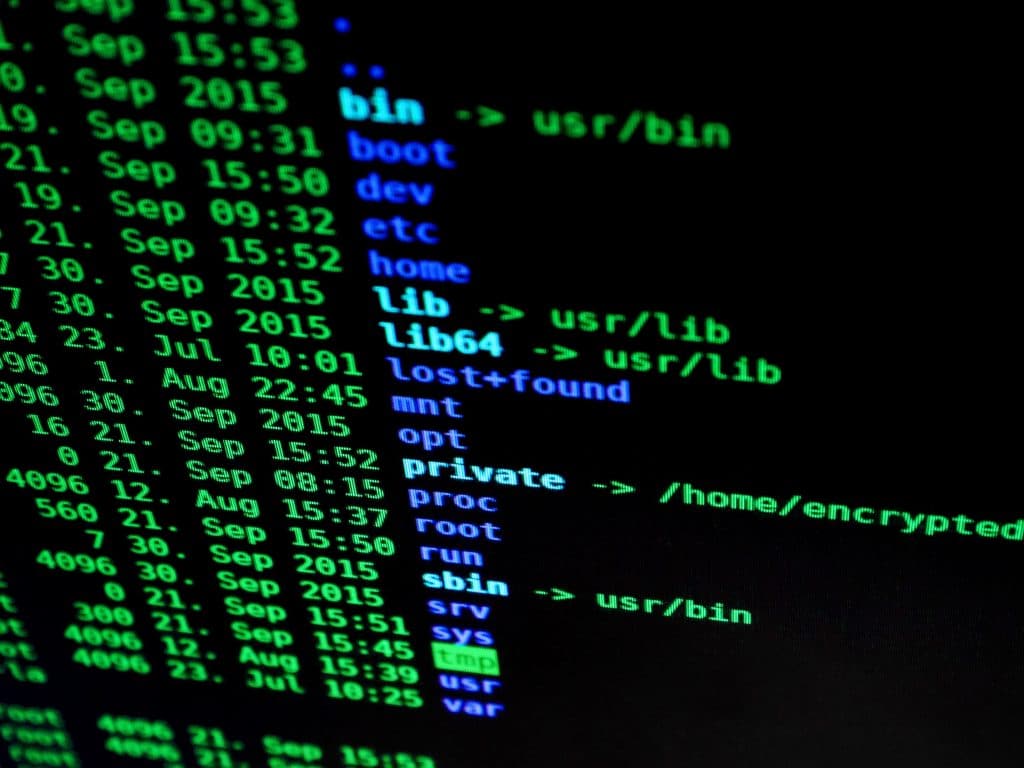
A firewall is an essential part of a security strategy that keeps track of and manages network traffic in accordance with pre-established security rules. The internet and your company’s network are separated from one another by this barrier and your network security framework’s firewall serves as the first line of defense, assisting in the prevention of data breaches and cyberattacks.
Firewall protection is more than just a singular solution—it’s a range of defenses, each tailored to combat different kinds of security threats. From traditional firewall software to unified threat management (UTM) systems, businesses have a plethora of choices to secure their network. A well-implemented network firewall offers sophisticated features like an intrusion detection system (IDS), an intrusion prevention system (IPS), network traffic filtering, and much more.
Whether you’re a small business with a single server or a large enterprise with a sprawling campus network solution, understanding how a firewall protects your network is vital.
At the most basic level, all firewalls perform packet filtering. They inspect each packet of data that travels into or out of the network. The firewall checks these packets against its set of established firewall rules and decides whether to let the packet through or discard it. This process is similar to a bouncer checking IDs at a nightclub—the uninvited and underaged are turned away!
Beyond basic packet filtering, stateful inspection takes network protection up a notch. A stateful firewall keeps track of ongoing connections and understands the ‘context’ of network traffic. For instance, if a user on your network initiates a connection with an external server, the firewall will ‘remember’ this and allow return traffic from that server. Stateful inspection, thus, helps maintain the flow of legitimate traffic while blocking the suspicious ones.
Another way firewalls protect your network is through proxy services. In this scenario, the firewall acts as an intermediary (a ‘proxy’) between networks, effectively obscuring the details of the internal network from the outside world. Imagine having a personal assistant who handles all your interactions—you remain hidden while the assistant takes care of business. That’s what a proxy firewall does, adding an extra layer of protection and anonymity.
Without adequate firewall and network protection, enterprises are like open books—anyone can read them, misuse their information, and even rewrite their narratives. Network security breaches can result in data theft, financial loss, and severe damage to a company’s reputation.
Cyberattacks are a harsh reality in our connected digital world and all businesses are attractive targets for cybercriminals. Your company’s critical data is at risk if you don’t have a reliable network firewall, and firewalls offer protection from a range of dangers, including ransomware and other serious threats like Advanced Persistent Threats (APTs) and simple spam or adware.
For businesses, data breaches can have immediate financial consequences. Besides, data breaches can result in lost commercial prospects, legal penalties, and reputational harm to the company, but with firewall protection, you’re safeguarding more than just your network—you’re safeguarding the future of your company.
Now that we’ve established the importance of firewall and network protection, let’s delve into what qualities define the best network firewall.
A robust firewall needs to offer more than just the basics. It should include advanced features like an intrusion detection system (IDS), an intrusion prevention system (IPS), VPN support, and the ability to filter network traffic intelligently. The best firewall software can monitor and control application use, block or allow specific websites, and even detect and prevent the spread of malware.
The best network firewall must also be customizable to fit your specific business needs. It should be scalable to grow with your business and compatible with your existing network systems – a firewall that doesn’t play well with your current infrastructure could end up causing more problems than it solves. A good example of an adaptable solution is Sangfor firewall, which offers not just advanced security features but also the flexibility and scalability that modern enterprises need.
As technology evolves, so do cyber threats—and, consequently, our defense mechanisms. Traditional network firewalls, while reliable, may not be sufficient in the face of sophisticated attacks.
Next-generation firewalls (NGFWs), on the other hand, provide a more comprehensive and integrated approach to network security. They incorporate advanced technologies like application-level inspection and intrusion prevention systems to provide superior protection.
While both types of firewalls have their merits, the increasing complexity of cyber threats makes NGFWs the go-to choice for many enterprises.
Choosing the right network firewall is crucial for the safety and smooth operation of your business. Here are some steps to guide you through the process:
It is understandable that most businesses have unique network architecture and business requirements from one another. It is likely that this will lead to different requirements for security protection. Are you a small business with a single site or a large enterprise with multiple sites across the globe? Do you deal with highly sensitive information, such as financial data or health records? The answers to these questions will help guide your firewall selection.
The best network firewall should not only cater to your current needs but also be capable of handling future threats. Key features to look for include:
As your business grows, your network firewall should be able to scale with it. Therefore, look for a solution that can easily accommodate more users and manage increased network traffic.
Your chosen firewall should seamlessly integrate with your existing infrastructure. It should be compatible with your operating systems, network equipment, and any other security measures you have in place. This way, it can enhance your network’s security rather than cause configuration issues.
Consider the reputation of the firewall vendor. Companies like Sangfor that have a proven track record of delivering a quality firewall support solution should be at the top of your list.
Reliable customer support is essential. Ensure that the firewall provider offers comprehensive IT support services to help you during the installation, setup, and any future issues you might face.
The final factor in your choosing is your budget. Cost should be taken into account, but security should never be sacrificed. Choose a solution that provides the most value for your money, taking into account both the up-front cost and future savings from preventing security breaches.
Although selecting the ideal network firewall is not simple, you may find a solution that meets your company’s objectives and provides peace of mind by carefully weighing these considerations.
A network firewall is a security mechanism that regulates incoming and outgoing network traffic based on predetermined rules. Firewall support involves technical assistance in the setup, maintenance, and troubleshooting of firewalls. It ensures the smooth operation and optimization of firewall systems. On the other hand, firewall security management encompasses tasks such as policy definition, rule configuration, monitoring and auditing, change management, and security incident response. It aims to maintain the security posture of firewalls, aligning them with organizational policies and regulatory requirements.
Firewall support and firewall security management are interrelated components of network security. While support focuses on the technical aspects of maintaining firewalls, security management addresses the governance, configuration, monitoring, and incident response aspects. Together, they work towards creating a robust security infrastructure that protects networks from unauthorized access, malicious activities, and data breaches.
To illustrate the significance of firewalls, let’s look at three success stories from different sectors:
A mid-size healthcare provider was facing continuous attempts of cyberattacks, aiming to gain unauthorized access to sensitive patient data. The provider turned to a robust network firewall solution, capable of packet filtering and stateful inspection. The firewall was configured to scrutinize incoming and outgoing data packets, allowing only legitimate traffic. Since implementing the firewall, the healthcare provider has seen an 85% reduction in cyber threats and has successfully safeguarded patient data.
An e-commerce business was struggling with DDoS attacks that slowed its website and impacted customer satisfaction. The company opted for a next-generation firewall, equipped with Intrusion Prevention System (IPS), DDoS protection, and VPN support. This firewall provided the e-commerce platform with advanced protection, minimizing downtime, improving website performance, and maintaining customer trust.
A large university with a sprawling campus network faced the challenge of managing diverse network traffic, securing sensitive data, and providing students and staff with secure remote access. By implementing a campus network solution with an integrated firewall system, they achieved network segmentation, effectively isolating and protecting different network sectors. They also introduced a secure VPN service for remote learners and faculty, maintaining academic continuity without compromising on security.
These cases highlight the potential of network firewalls in addressing various industry-specific network security challenges. It is clear that with the right firewall, enterprises can protect their operations, maintain customer trust, and ensure business continuity.
In conclusion, a network firewall is a non-negotiable asset in any enterprise’s cybersecurity arsenal. Whether you’re a small business or a sprawling enterprise, investing in a robust, scalable, and feature-rich firewall such as the Sangfor firewall is crucial to safeguarding your network and protecting your business’s future.
Ready to explore what managed IT services can do for your business? THREE IC has the expertise, thanks to our campus network solution, Ruijie, our partner security solution from Sangfor, and our IT support services, which will all give your organisation a reliable and top-of-class security posture. Contact us today for a comprehensive discussion on how you can harness the power of a leading MSP to streamline your operations and improve your digital connectivity and cybersecurity. Ensure your enterprise is always protected, and always ahead.
A network firewall forms the first line of defense in a comprehensive network security policy. It helps enforce the policy rules by scrutinizing network traffic and either permitting or denying it based on pre-established firewall rules. It works in conjunction with other security measures like Intrusion Detection Systems (IDS), Intrusion Prevention Systems (IPS), and network access control systems.
Unified Threat Management (UTM) refers to a security strategy that brings together multiple security tools into a single platform, including a firewall, anti-virus, anti-spam, VPN, and intrusion detection. Working alongside a network firewall, a UTM enhances overall security, simplifies management, and reduces potential protection gaps.
Network segmentation divides a network into smaller parts or segments. Each segment can have its own set of firewall rules and policies, which can limit the spread of cyber threats across the network. This way, even if one segment is compromised, others remain secure, adding another layer of defense to the overall network security.
Next-generation firewalls (NGFWs) build upon traditional firewalls by offering more sophisticated and targeted protection. They integrate traditional firewall protection with additional features like intrusion prevention, application-level inspection, and identity-aware security policies. This level of advanced protection is crucial in today's complex threat landscape.
A Virtual Private Network (VPN) provides a secure connection for remote users to access the network. Firewalls play a key role in this process by inspecting VPN traffic, applying security policies, and ensuring that only authorized users can access the network. This maintains network integrity while enabling flexible remote access.

THREE IC, a prominent provider of Cyber Security and IT solutions, produces the majority of the blog posts featured here. These articles are authored by a team of professionals employed at THREE IC, including content writers and marketing experts. They are dedicated to creating informative content on a wide range of subjects that are relevant to our readers.
Our team ensures that the published articles are accurate and beneficial for our clients and partners, helping them stay informed about the latest trends in Cyber Security and IT and understand how these advancements can benefit their organizations.

address
address
TEL
+65 XXXX XXXX
info@threeic.com
address
Singapore Address here
address